ISACA Jacksonville · April 17, 2026 · Session 2
From Alert Triage
to Threat Hunting
to Threat Hunting
What AI Is Actually Doing
in the SOC Today
in the SOC Today
Nathan Burke
Chief Marketing Officer · 7AI · nate@7ai.com
Dennis Friedley
Account Executive · 7AI · dennis.friedley@sevenai.com · 727-688-6724
Chief Marketing Officer · 7AI · nate@7ai.com
Dennis Friedley
Account Executive · 7AI · dennis.friedley@sevenai.com · 727-688-6724
Today’s Session
01
The threat has already changed
02
What AI is actually doing in the SOC
03
What happens to the humans
04
What comes next
But first,
a story.
The Emerging Archetype
Chief Innovation
Security Officer.
Security Officer.
The conversation has shifted from the promise of AI to the production of outcomes. The CISOs leading that shift aren’t just securing AI. They’re using security as the proof point that earns them a seat at the strategy table.
Top 30 for 2025
blog.7ai.com
Top 30 for 2026
blog.7ai.com
.png)
The Problem
The Alert Problem Is
Unsolvable By Humans Alone.
Unsolvable By Humans Alone.
Security operations hasn't changed its fundamental model: alerts still flow to analysts. Every tool — including AI — still terminates at a human. The volume has outpaced the workforce. Permanently.
The issue isn't the tools. It's that humans are still doing work that machines should handle — and machines aren't equipped to do work that requires human judgment.
1,000+
Alerts the average SOC analyst is expected to handle per day.
65%
Of SOC analysts considering leaving the field due to alert fatigue.
4M
Unfilled cybersecurity positions globally — and the gap is growing.
This Week
Meet Mythos.
Anthropic just released Claude Mythos — a purpose-built AI model for offensive security. The gap between vulnerability discovery and active exploitation has collapsed to minutes. AI now handles 80–90% of tactical offensive operations autonomously.
"The beginning of the end of cybersecurity."
— Jen Easterly, Former CISA Director



The Threat Landscape
AI-Enabled Offense Is Already Here.
Russia · FANCY BEAR
AI IN
MALWARE
MALWARE
LAMEHUG
An LLM embedded directly into active malware — autonomously generating reconnaissance commands. The first nation-state AI weapon, not a development tool.
eCrime · Phishing
AI AT
SCALE
SCALE
Quishing Campaigns
Per-recipient unique QR payloads that bypass email filters. The URL changes at any time — the infrastructure outlives any single attack.
Mandiant M-Trends 2026
22
Seconds to lateral movement
Down from 8 hours. Any defense relying on humans to process every alert in that window has already lost.
North Korea · Bybit
$285M
In 10 seconds
Lazarus Group. Six months of patient reconnaissance. Machine-speed execution at the moment of strike. Human defenders had no chance.
The Market Moment
The Question
Has Changed.
Has Changed.
One year ago, every meeting started with skepticism. Today, security leaders aren't asking whether AI works in the SOC. They're asking how to operationalize it — and how fast.
2023
"Does AI actually work in security?"
2024
"Wait—could copilots actually make us faster?"
Early 25
"What should our AI strategy actually look like?"
Today
"How long do I have? How do I get agents into production now?"
The Noise
Everyone Claims AI.
Not Everyone Delivers Agentic.
Not Everyone Delivers Agentic.
The Copilot
Embedded Helpers
AI that assists analysts — but every decision still requires a human. Most "AI in security" tools on the market today.
Microsoft Security Copilot, CrowdStrike Charlotte AI
The Playbook
Task Automation
Playbook execution with AI bolted on. Still requires humans to build and maintain every workflow for every scenario.
SOAR platforms, AI-enhanced automation tools
Where 7AI operates
Agentic SOC
AI agents investigate, respond, and hunt autonomously — every alert, around the clock. No playbooks. No human-in-the-loop for every decision.
DXC, BigID, Blackstone — in production
About 7AI
One Year.
Here's What We've Learned.
Here's What We've Learned.
302
Days from stealth to Series A.
$130M
Series A — led by Index Ventures.
#1
World's largest agentic security deployment.
DAYS
From first investigation to full production.
Founded 2024 by Lior Div (CEO) and Yonatan Striem-Amit (CTO). | 5M+ alerts processed. | Channel-first GTM via GuidePoint, AWS, and strategic partners.
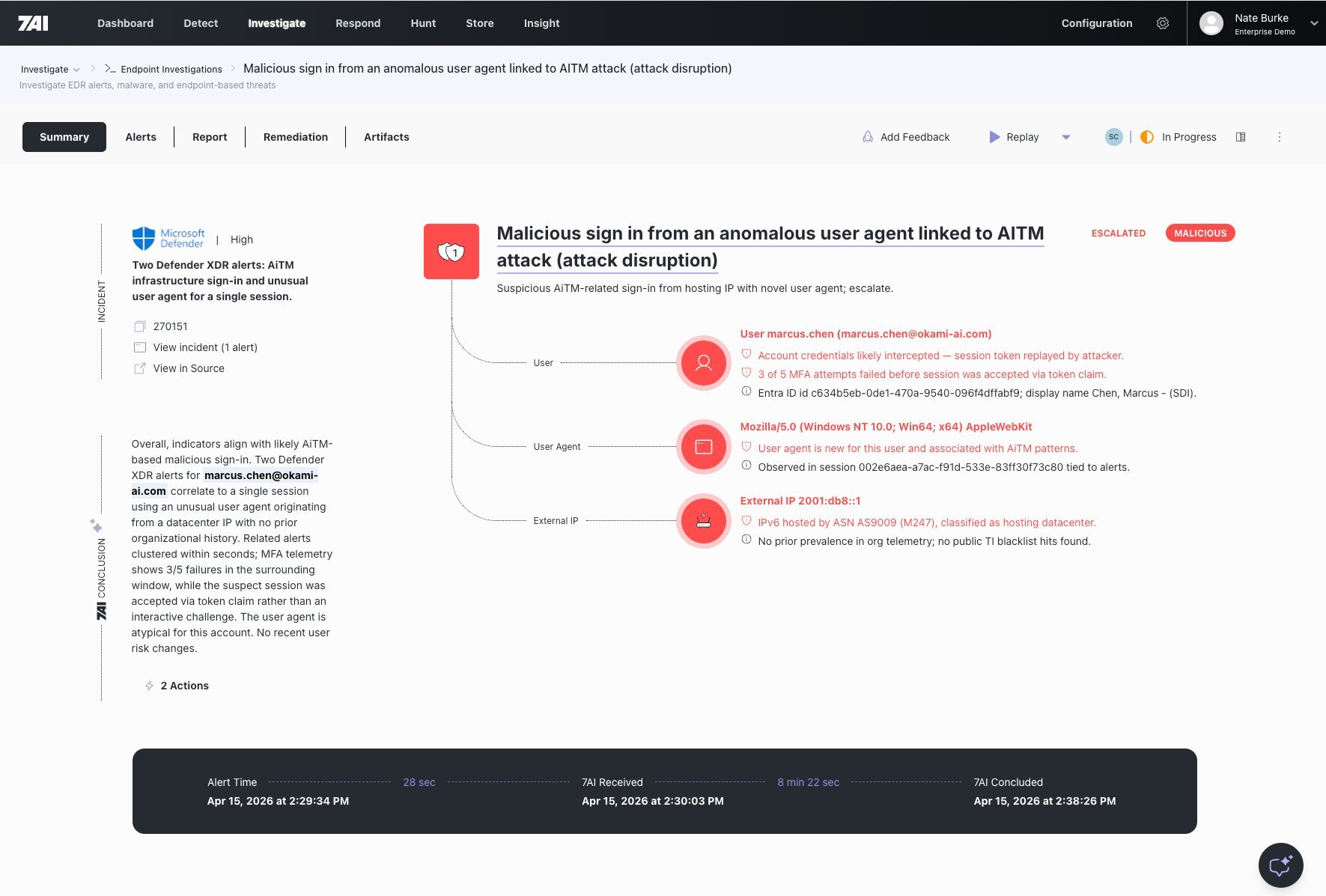
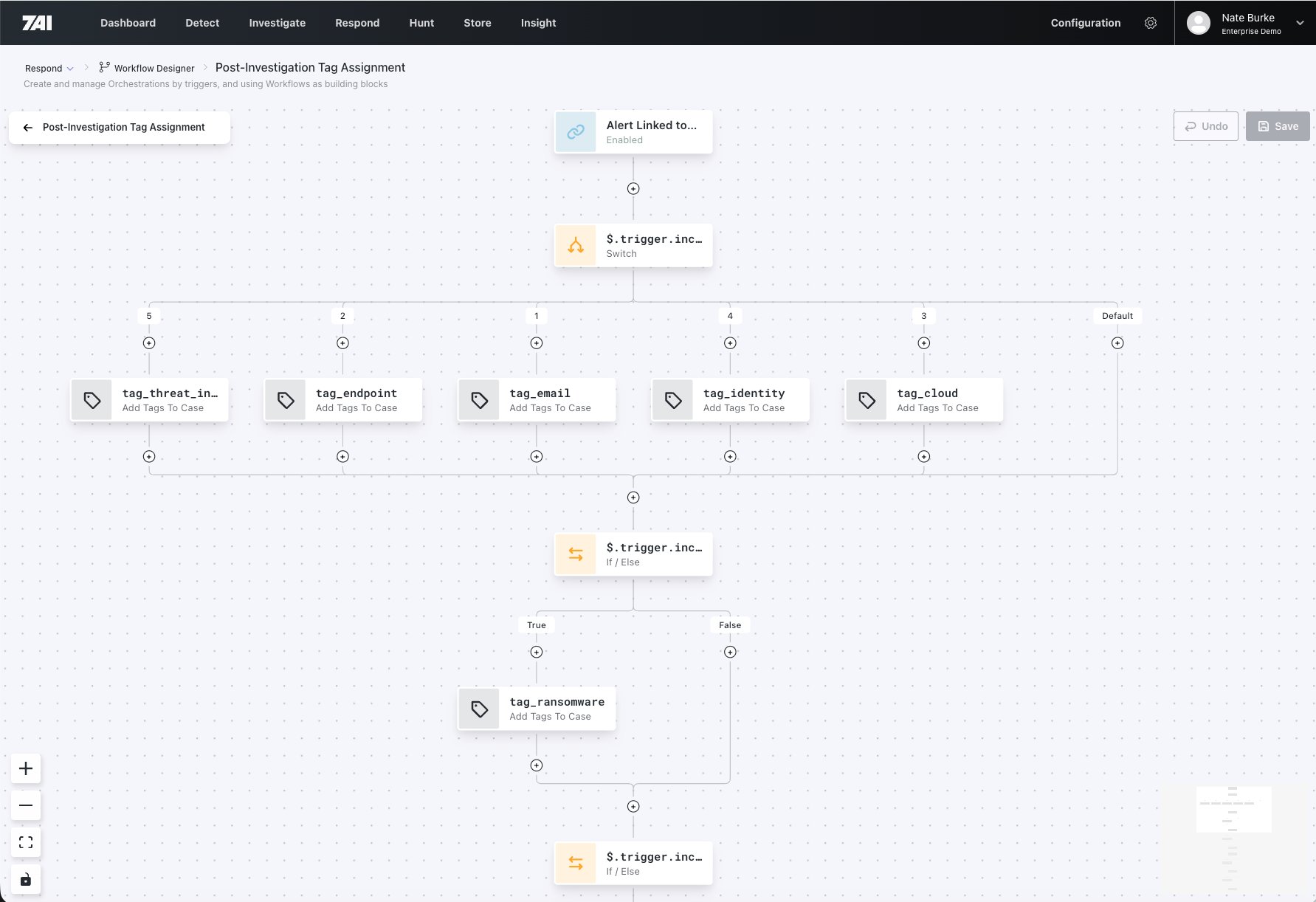
PLATFORM 01 / 05
Investigations
AI-Powered Analysis
When an alert fires, swarming AI agents spring into action — enriching data, querying your environment, correlating across systems, and forming conclusions. Hours become minutes.
- Autonomous enrichment & correlation
- Multi-system data gathering
- Conclusions with full evidence trail
- Complete investigation narrative
→ Next: Detection
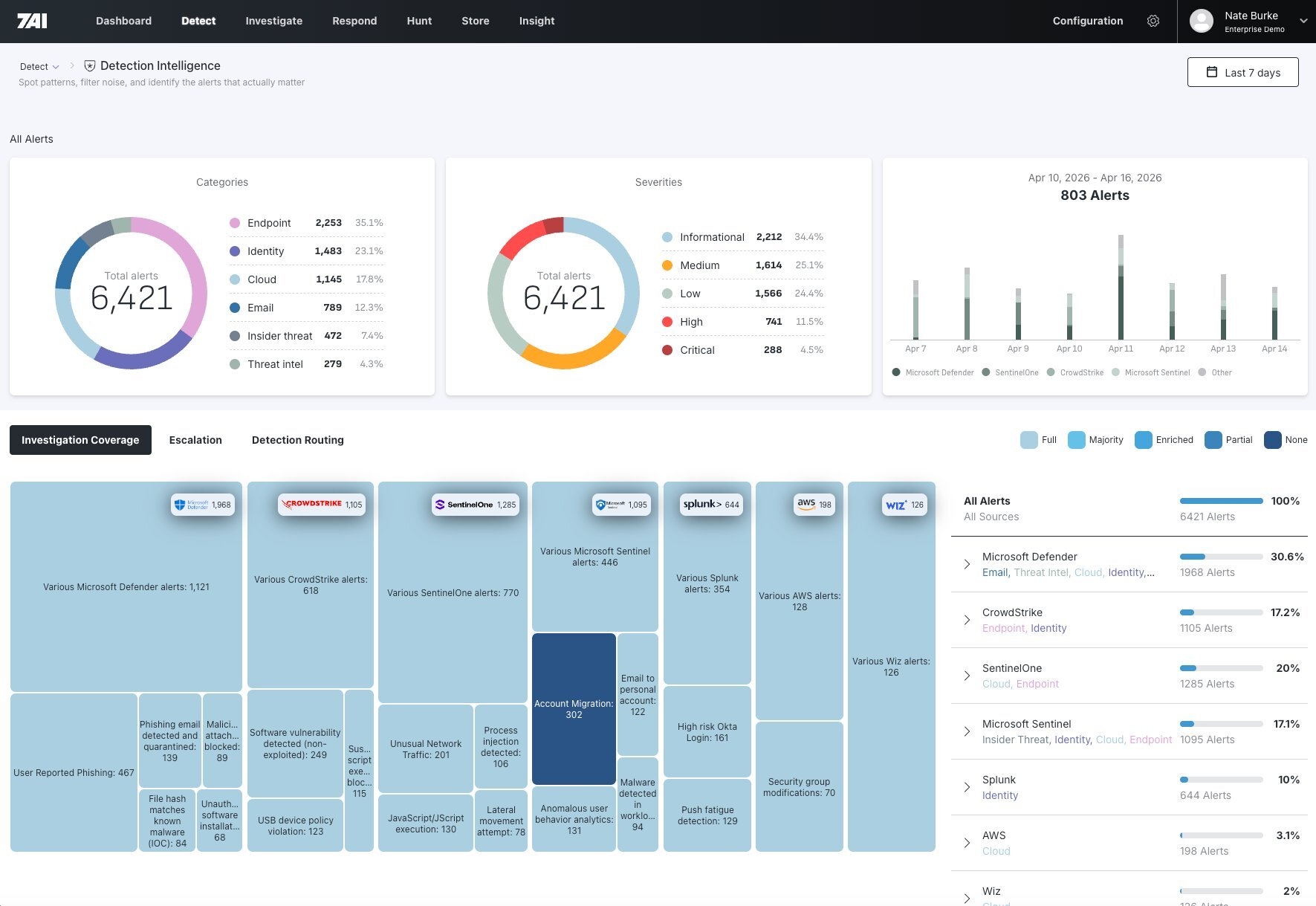
PLATFORM 02 / 05
Detection
Intelligent Alert Processing
7AI ingests alerts from your security tools, applies AI-powered analysis, and delivers only what matters. Instead of drowning in thousands of alerts, your team sees actionable conclusions.
- Multi-source alert ingestion
- AI-powered triage & enrichment
- Up to 95–99% false positive elimination
- Context-aware conclusions
→ Next: Response
PLATFORM 03 / 05
Response
Customized Remediation
Flexible remediation options to take action based on investigation conclusions — not just predefined playbooks. Isolate endpoints, disable accounts, block IPs, trigger custom workflows.
- Conclusion-driven actions
- Native integrations for containment
- Human-in-the-loop options
- Full audit trail
→ Next: Hunting
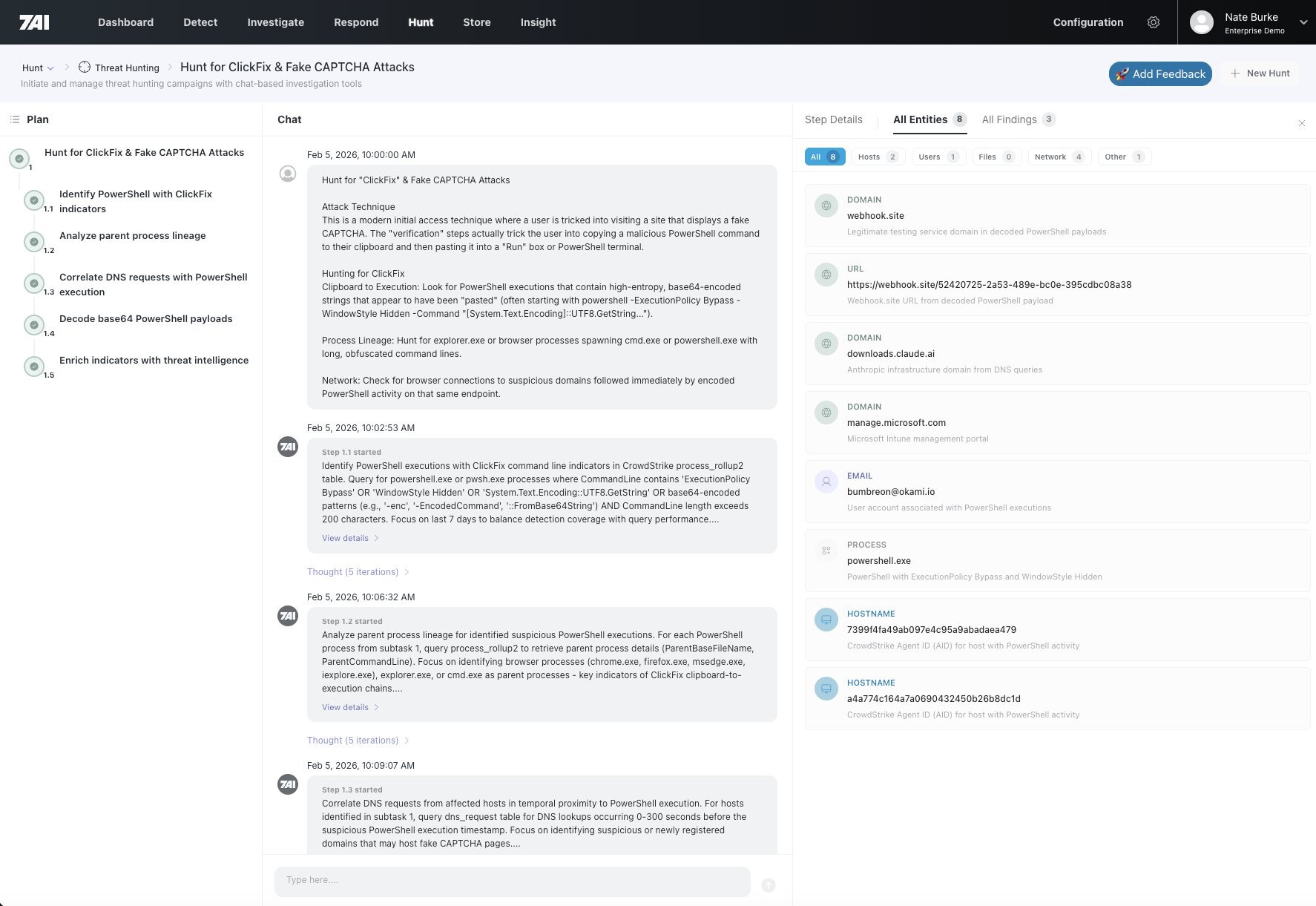
PLATFORM 04 / 05
Hunting
Proactive Threat Search
With AI agents handling alert triage, your analysts are free to hunt. 7AI provides powerful threat hunting capabilities to uncover threats hiding in your environment before they fire alerts.
- Cross-system threat correlation
- AI-powered hunt suggestions
- IOC extraction
- Historical pattern analysis
→ Next: Collaboration
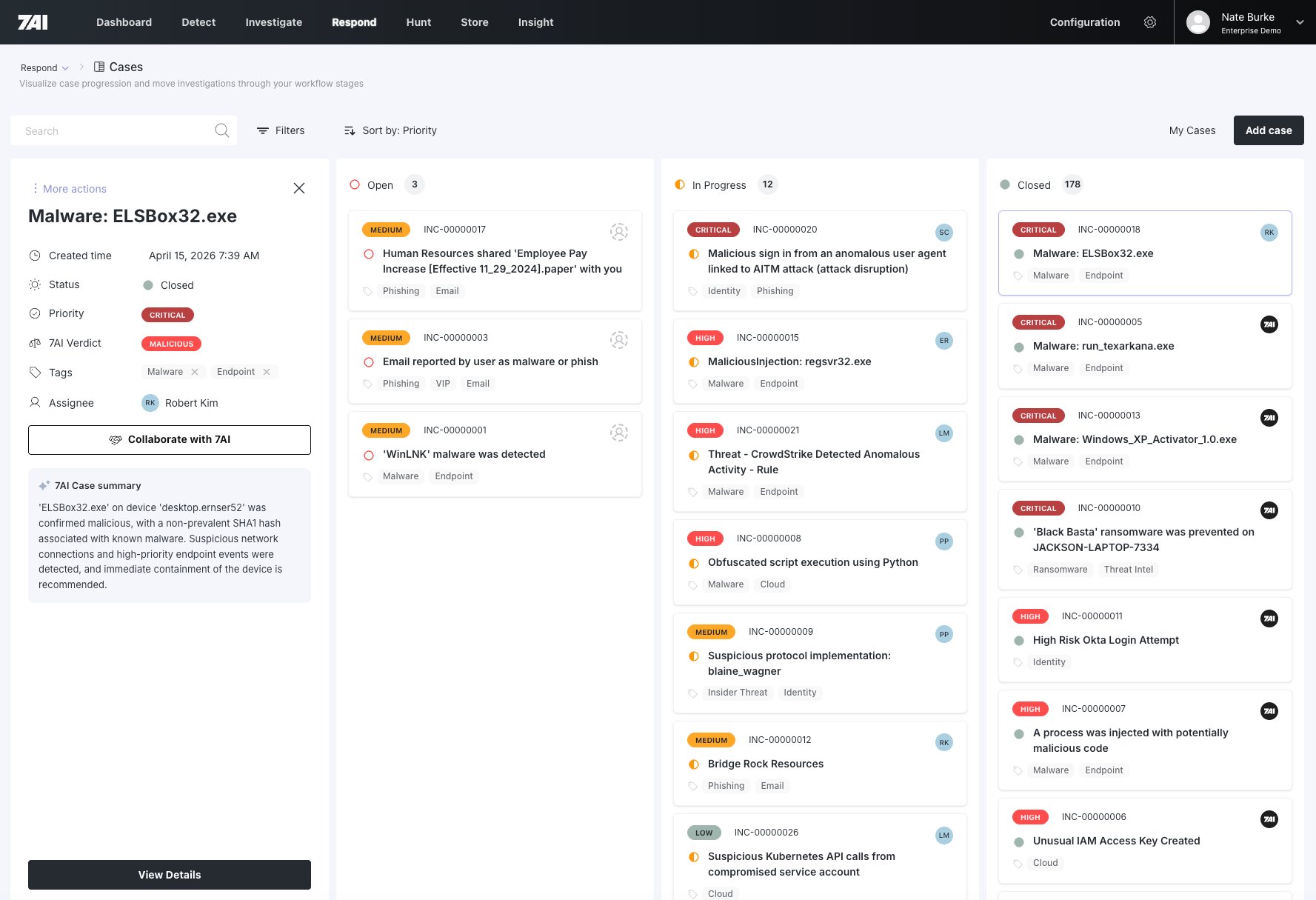
PLATFORM 05 / 05
Collaboration
Unified Incident Management
A single source of truth for every security incident. AI agents automatically populate cases with investigation findings, correlate related alerts, and maintain a complete audit trail.
- Auto-populated investigation summaries
- Cross-alert correlation
- Evidence collection & chain of custody
- Team collaboration & handoffs
Deployment Model
How Customers Use 7AI.
SOC
+ 7AI
+ 7AI
"We need to investigate faster without adding headcount."
SOC
↑
7AI
↓
↑ Alerts
E
Reviews all tickets and makes decisions.
Enrichment
SOC
+ Use Cases
+ Use Cases
"We want to hand some SOC work to 7AI."
SOC
↑
7AI
↓
↑ Alerts
EC
Focuses on use cases worth their time.
Conclusions
Enrichment
MDR
+ 7AI
+ 7AI
"MDR doesn't cover all our use cases."
SOC
↑
7AI
↓
ECR
SOC
↑
MDR
↓
ECR
Works with MDR + 7AI for full coverage.
Response
Conclusions
Enrichment
MDR
"We are looking to replace our MDR."
SOC
↑
7AI
↓
↑ Alerts
E
C
R
P+
Handles oversight only.
PLAID +
Response
Conclusions
Enrichment
Customer Highlight — Scale
DXC Technology
IT Outsourcing
120,000 Employees
“
Right off the bat we’ve seen an 80% reduction in tier 1 analyst time. As those tickets progressed through the funnel, we’ve seen easily a 95–99% reduction in the tickets that human beings have to look at. Incredible outcome.
We believe this is the world’s largest, most successful AI SOC deployment.”
We believe this is the world’s largest, most successful AI SOC deployment.”
Mike Baker · CISO, DXC Technology
95–99%
Reduction in tickets requiring human review.
80%+
Reduction in Tier 1 analyst time.
8 Weeks
From first conversation to global deployment across 25 delivery centers.

Mike Baker
CISO, DXC Technology
Customer Highlight — Capacity
BigID
Security Software
1,000 Employees
“
I’ve envisioned this for five years — AI handling the mundane alert triage so my team could focus on creative, strategic security work. 7AI made it real, scaling our team’s capacity 10x and freeing analysts from burnout to work on the interesting challenges that actually matter.”
Kyle Kurdziolek · VP Security, BigID
10X
Team capacity increase.
5:20
Average AI investigation time.
47 Min
Faster than previous MDR provider.

Kyle Kurdziolek
VP Security, BigID
The Human Question
This Isn't About Replacement.
It's About Elevation.
It's About Elevation.
The question every security leader actually wants to ask isn't "will AI take my team's jobs?" It's: what should my analysts be doing in a world where AI handles execution?
The emerging role is AI orchestrators — people who excel at human-agent teaming. That's exactly what we see in production. People don't lose their jobs. They stop doing non-human work.
01
Before 7AI
Tier 1 analysts spend 60–80% of their day on alert triage, enrichment, and documentation — work that requires no human judgment. Burnout is structural, not personal.
02
After 7AI
Those same analysts hunt threats, investigate what matters, and manage how security operations actually work. They lead the AI instead of being buried under it.
03
The Shift
Your people move from doing the work to leading the AI that does the work. That's a career upgrade — and what makes an agentic SOC sustainable.
What Good Looks Like
The Mindset Shift That Changes Everything.
The Setup
A mid-market software company. CISO skeptical. When 7AI took over Tier 1 work, his analysts didn't lose their jobs — they got their time back.
→
The Question That Changed Everything
"What else am I doing
that a machine should be doing?"
that a machine should be doing?"
The Discovery
Security questionnaires. 98 questions per intake. 3+ hours of manual work every time. Pure non-human work — hiding in plain sight.
→
The Result
25
Minutes with AI
98
Questions answered
3+ hrs
Saved per intake
The Takeaway
Not "will AI take my job" — but "what non-human work am I still doing, and why?" When analysts stop doing non-human work, they start doing the human work that actually advances your security program.
Our Model
PLAID: People-Led, AI-Driven.
Out-of-the-box AI is good. AI that understands your environment, your workflows, and your exceptions is unstoppable.
People-Led
→
Elite AI Security Engineers embedded with your team
→
Deep understanding of YOUR environment — your tools, your exceptions, your risk tolerance
→
Custom configurations for your specific workflows and use cases
→
Continuous optimization and named accountability
AI-Driven
→
Dynamic agents that learn and adapt to your environment
→
Machine-speed investigations 24/7 — every alert, every time
→
Consistent, explainable conclusions with full documentation
→
Scalable across unlimited alert volume with no additional headcount
The Result: A Partnership, Not a Product
You don't get a black box. You get expert humans who configure AI agents to work exactly how you need — then continuously improve them. Days to production, not months.
The Frontier
Threat Hunting Is Where This Goes.
01
Proactive Discovery
Our threat research team recently found a full-scale phishing campaign at a healthcare customer before a single alert fired. Agents hunted outward from one AI-escalated investigation. The human team had capacity to act because they weren't buried in triage.
02
Intelligence-Driven Hunting at Machine Speed
New threat intelligence report → AI runs it across your entire environment → verdict in under 20 minutes. In March, we found confirmed hits at multiple customer environments against a major supply chain compromise — faster than commercial threat intel providers flagged the exposure.
03
The Parity Equation
When AI handles detection, investigation, and response continuously, you accumulate months of context — every entity, every behavior, every pattern. That context is what makes threat hunting genuinely proactive. Attackers are building this capability. The question is whether defenders will too.
The Moment
The Parity
Window Is Open
Right Now.
Window Is Open
Right Now.
Defenders have access to the same transformative AI technology as attackers — at the same moment in history. That has never been true before.
After RSA, the question we heard from CISOs wasn't "does AI work in the SOC?" The question was: "How long do I have?"
The organizations that act now will have months of production data, tuned agents, and operational maturity before their peers start evaluating vendors.
After RSA, the question we heard from CISOs wasn't "does AI work in the SOC?" The question was: "How long do I have?"
The organizations that act now will have months of production data, tuned agents, and operational maturity before their peers start evaluating vendors.
The question is whether you use it.
What We Covered
01
The threat has already changed
Mythos. LAMEHUG. 22 seconds. Attackers are already operating at machine speed.
02
What AI is actually doing in the SOC
5M+ investigations. 95–99% false positive reduction. 8 weeks to global deployment at DXC.
03
What happens to the humans
Not replacement. Elevation. L1 analysts becoming L2. CISOs becoming Chief Innovation Security Officers.
04
What comes next
The parity window is open now. The organizations that act have a head start that compounds.
Questions?
Thank You.
Nathan Burke · CMO, 7AI · nate@7ai.com
Dennis Friedley · Account Executive, 7AI · dennis.friedley@sevenai.com · 727-688-6724
7ai.com
Dennis Friedley · Account Executive, 7AI · dennis.friedley@sevenai.com · 727-688-6724
7ai.com